Every SOC team has a version of the same uncomfortable question sitting in the back of their mind: if an attacker used this technique right now, would we actually detect it?
Most of the time, nobody has a clean answer. You have detection rules, you have a SIEM, you have a rough sense that your coverage is decent, but mapping exactly what you can and can’t detect against the MITRE ATT&CK framework is tedious work. The official ATT&CK Navigator is powerful, but getting your actual detections into it requires manual T-code tagging, which means it either never gets done or gets done once and never maintained.
I built MITRE ATT&CK Map to fix that. Upload your Sigma rules or paste a detection list, and the tool maps your coverage across ATT&CK Enterprise and MITRE ATLAS automatically. You get a colour-coded matrix in seconds.
It’s live at mitre-attack-map.vercel.app and the source is on GitHub.
The Problem With Manual Coverage Mapping
The MITRE ATT&CK Navigator is the go-to tool for visualising coverage. It’s well built and widely used. But the workflow to actually use it meaningfully looks like this:
You export your detection rules, go through them one by one, identify which T-codes they map to, manually build or update a Navigator Layer JSON, load it, and then realise half your Sigma rules don’t have explicit ATT&CK tags so you’re guessing at mappings. Then you do it again next quarter when new rules are added.
That process works if you have dedicated time and a small ruleset. In a real environment with hundreds of Sigma rules across multiple platforms, it’s a maintenance nightmare. Coverage maps go stale fast, and a stale coverage map gives you false confidence.
What the Tool Does
Upload Your Detections, See Your Coverage
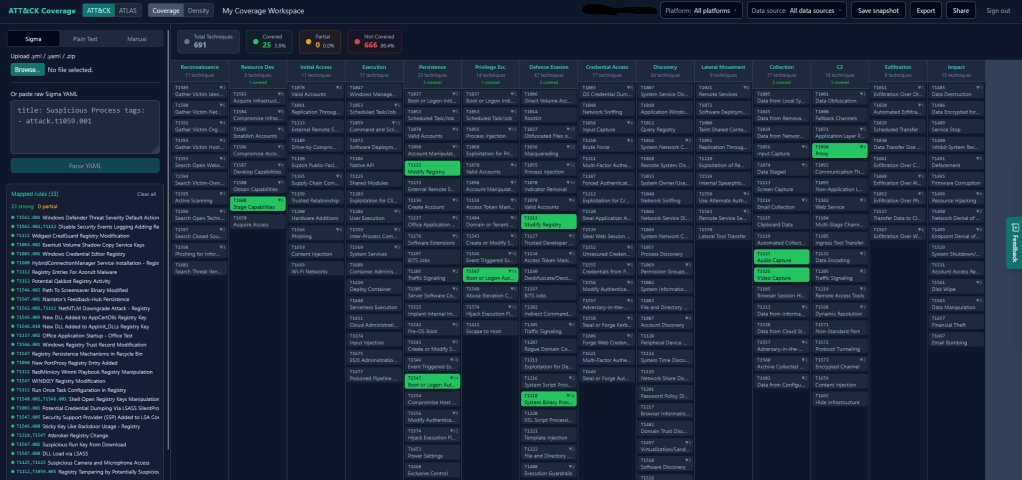
You can bring your detections into the tool three ways:
- Drop in a Sigma YAML file or ZIP — bulk upload, recursively parsed
- Paste a plain-text list of rule names or T-codes
- Pick techniques manually from the full ATT&CK and ATLAS catalogue
Once ingested, covered techniques turn green, fuzzy-matched ones turn amber, and blind spots stay grey. You get a clear picture of where you stand without doing any manual T-code work.
Sigma-Native Parsing
The parser reads attack.t1059.001 and atlas.aml.t0000 tags directly from your Sigma rules. For rules that don’t have explicit ATT&CK tags, it scans for T-codes in the rule content, then falls back to keyword matching against technique names. So even a partially tagged ruleset gives you something useful to work with rather than nothing.
ATT&CK and ATLAS Together
Most coverage tools focus on ATT&CK Enterprise and treat MITRE ATLAS (the adversarial AI/ML threat matrix) as an afterthought. This tool handles both in the same workspace. If you’re running ML models in your environment, which most cloud-heavy organisations are understanding your ATLAS coverage is increasingly relevant. You upload your rules once and check both frameworks without switching tools.
Always Current Data
ATT&CK and ATLAS data pull straight from the MITRE GitHub repos each time you open the tool. You always get the latest techniques without any manual updates or version management on your end.
Navigator Layer Export
When you’re done, you can export a v4.5 Layer JSON that loads directly in the official MITRE Navigator. Covered techniques get a score of 100, fuzzy matches get 50. Useful for reporting, sharing with leadership, or feeding into a red team planning session.
Workspace Snapshots and Sharing
Save your coverage state at any point and come back to it. With InstantDB configured, snapshots sync across devices and each workspace gets a shareable URL — so you can send a link to a colleague or a CISO without exporting anything.
Runs in Your Browser
Your rules and detections stay on your machine. There is no server processing your Sigma files. If you want cross-device sync or shareable links you can connect an InstantDB app, but the core tool works entirely client-side.
Who This Is For
If you’re a detection engineer trying to communicate coverage gaps to leadership, this gives you a visual you can actually put in front of people. If you’re a SOC analyst trying to understand which ATT&CK techniques your team is blind to, this shows you in seconds rather than hours. If you’re preparing for a purple team exercise and want to know which techniques to prioritise, filter the matrix and export a layer for your red team.
It’s also useful as a recurring health check. Run it against your current ruleset every time you do a detection review sprint, and you’ve got a before/after comparison showing what you’ve improved.
Built With Claude Code
This is the second tool I’ve shipped using Claude Code, and the build experience was similar to CloudComply, fast, and genuinely useful for handling the parts that would otherwise slow you down.
The Sigma parsing logic in particular, handling multiple input formats, fuzzy matching for untagged rules, recursive ZIP parsing, and then correctly resolving technique IDs across two different MITRE frameworks, would have taken weeks to architect and test manually. Claude Code handled the heavy lifting on that while I focused on what the tool actually needed to do.
Playwright MCP was back in the mix for UI work as well. Same as last time, UI fixes and layout adjustments that would have cost me hours of reading documentation took minutes.
Get Started
The app is live at https://mitre-attack-map.vercel.app
Source code is available for anyone to run locally or to rebuild https://github.com/cybersecbalaji/mitre_attack_map
Drop your Sigma rules in and see where your gaps actually are. If you have feedback, find a parsing issue, a technique that’s mapping incorrectly, or you want to suggest something, drop a comment below or raise an issue on GitHub.
More coming.

Leave a comment